Service Offerings
- Cyber security training
- Product reviews
- Blog or article writing
- SME & UHNWI cyber security
Chapter Author
Contact Graeme
Journalists, students or potential clients:
graeme@datasecurityexpert.co.uk
Something private to say?
PGP public key
graeme@datasecurityexpert.co.uk
Something private to say?
PGP public key
No AI Used Here

eDéjà Vu: Mossack Fonseca (Panama Leaks) and sudden switch to Incapsula
- Details
- Category: Blog
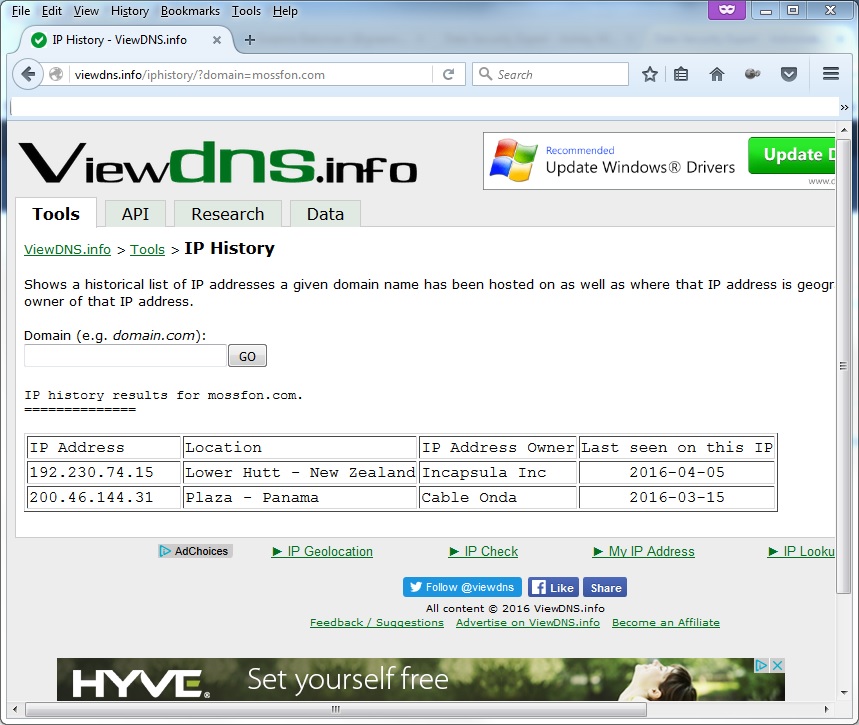
Mossack Fonseca has done exactly the same among reports their website was to blame for the intrusion and leak.
CloudFlare and Incapsula (rivals) are cloud WAF (web application firewall) service providers.
Pulling apart a mass market personalised malware debt invoice email
- Details
- Category: Cyber Security (Personal)
Today I received a decent attempt at personalising a malware email which would likely convince most people though not me of course! Think about it if the below would convince the average business or IT user then spear phishing would have nearly a 100% chance of working if planned and executed correctly.

Good it maybe, there are some giveaways: from a "prize company" not a debt collection agency, subject is my name which could say debt for Graeme Batsman, GBP not £, Danish URL for a British debt, my post code could be on a new line and no full stop on the final line.
Mossack Fonseca: how can you protect your digital crown jewels to an extremely high level?
- Details
- Category: Cyber Security (Personal)
Imagine you are a London law firm dealing with large charities, universities, large businesses, wealthy individuals and the head of state, not the prime minister David Cameron but Queen Elizabeth II. The first set of clients need good protection, more than those of a standard British law firm and Queen Elizabeth II would need top notch protection, potentially up a government rating of Secret or even Top Secret. On top of this only a few senior partners would deal with the client and their background checks would be higher.
Page 31 of 61

